Access Under Control
Centralized control of roles, rights, and access. Bare.ID ensures clear structures in access management and provides lasting support for IT and compliance officers.

Permissions Under Control. Risks Under Control.
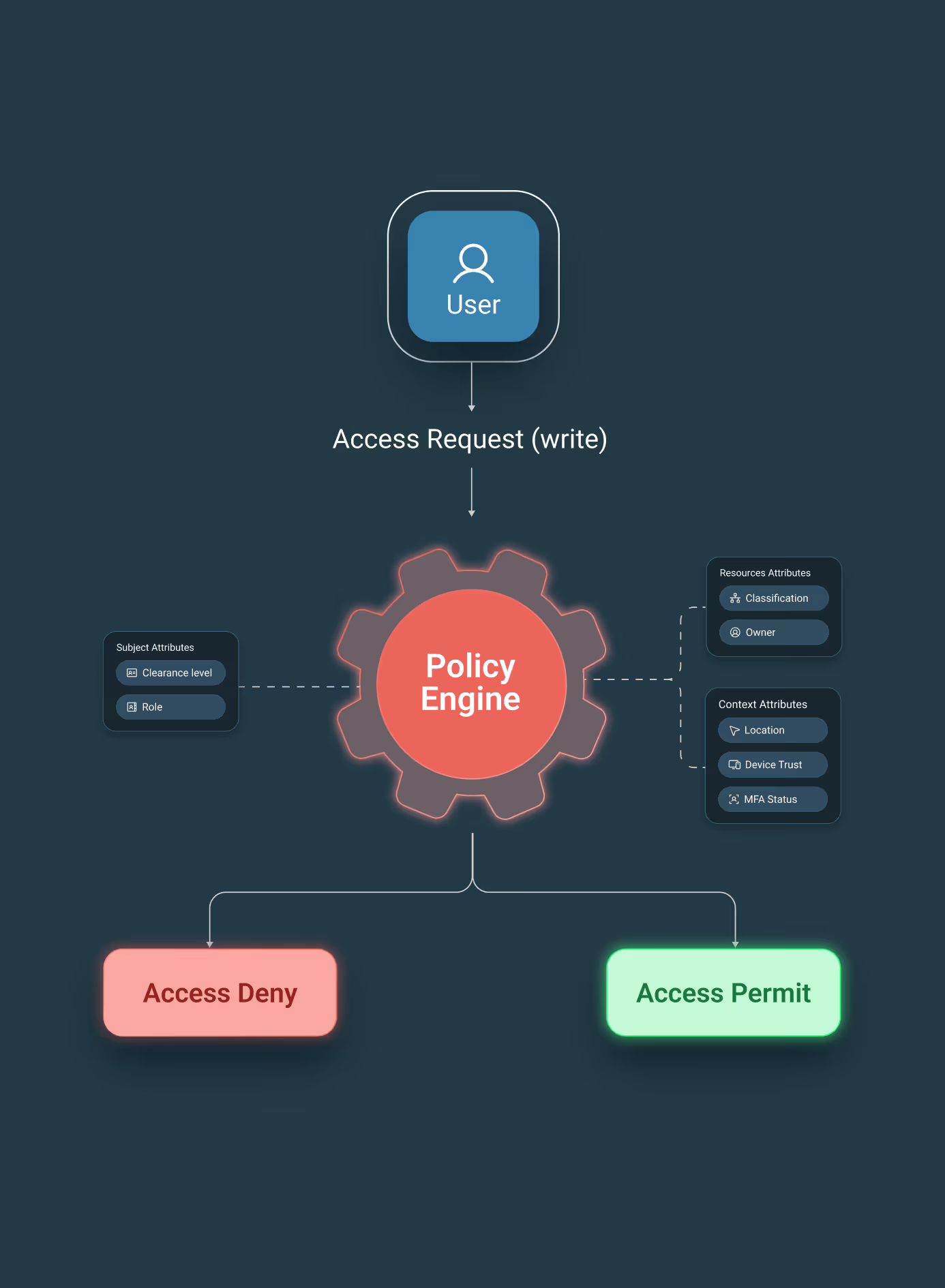
Access to applications determines how truly secure your IT is. Access Management is therefore a central control point of Bare.ID's IAM platform. It defines who can access what – and under what conditions. Centrally managed roles, rights, and policies prevent role sprawl and shadow IT.
Stay in control – instead of chasing it.

The advantages at a glance
Transparent Access Control
With Bare.ID, you manage roles and access rights centrally within your IAM platform. Orphaned accounts and over-privileged rights become visible and can be specifically corrected – across all applications.
Regulatory Requirements Considered
Bare.ID also embeds governance in Access Management: Clear role models, regular access reviews, and traceable policies support the implementation of regulatory requirements such as GDPR or ISO27001.
Rule-Based Instead of Gut Feeling
Bare.ID ensures that access is granted according to clear rules, not gut feeling. Decisions are traceable and repeatable – without manual case-by-case logic in IT. This increases security and relieves the IT department.
What is Access Management?
The part of IAM that determines what users are actually allowed to do. Access Management centrally controls which individuals or systems are allowed to access which applications, data, and functions. It defines and enforces roles, rights, and policies, including governance, audit mechanisms, and traceable control.
While Identity Management determines, who someone is, Access Management determines, what this identified person is allowed to do.

Features at a Glance
Modern Access Management not only ensures security but also clarity and efficiency. With our features, you stay in control.

It gets even better:
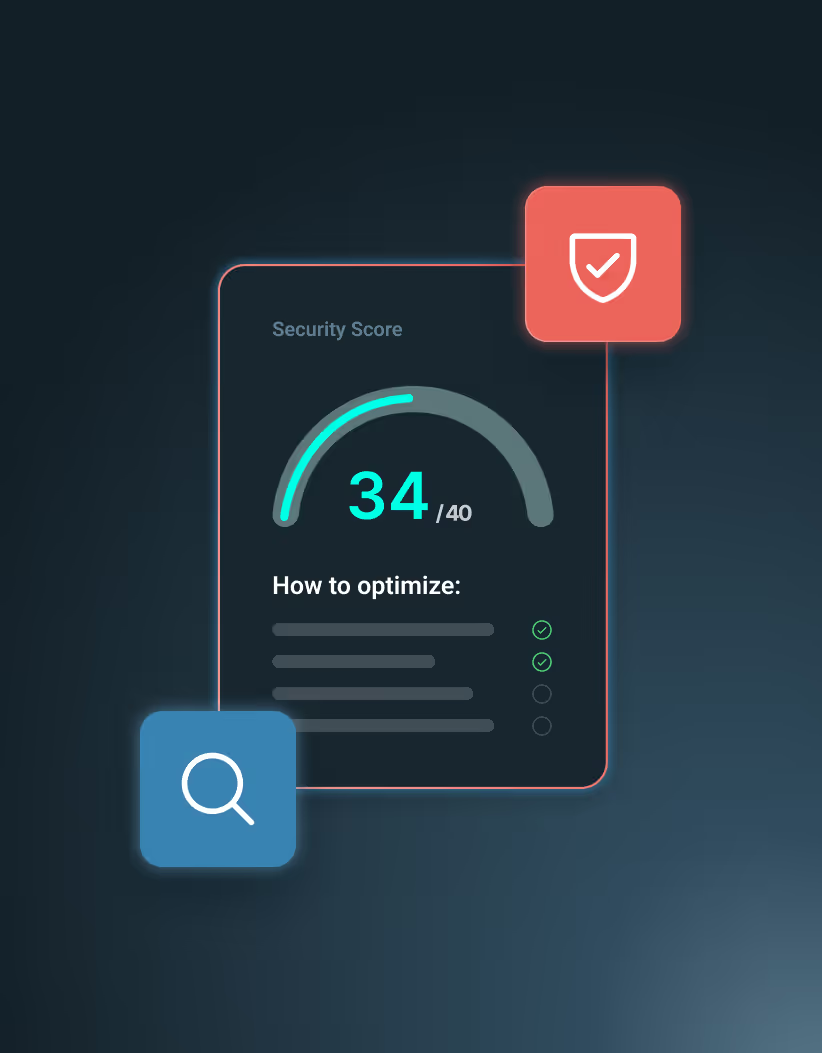
AI-powered IAM
Bare.ID enables AI-powered analyses to make patterns, risks, and anomalies in identities, roles, and permissions visible. The AI function supports admins in security-relevant decisions – especially where traditional rules reach their limits with complex structures and large user numbers.
Proactive security monitoring
Log analysis & troubleshooting
Role and permission analysis
Access Management with Bare.ID
Access Management that works for everyone – from IT to data protection officers.
Permissions managed. Organization managed.



The need for explanations ends.
Accountability begins.



Complexity out. Control in.



Compliance pressure? No problem with Bare.ID.
Bare.ID ensures that identities, access, and authentication processes comply with regulatory requirements. We cover all relevant requirements from GDPR, ISO 27001, NIS2, and DORA in the area of Identity & Access Management. This makes compliance a completed task – instead of an ongoing project on your to-do list.

ISO 27001:2022
Certified

DORA
Compliant

GDPR
Compliant

NIS 2
Compliant
Interested?
Let's talk.

FAQs
Still have questions? Feel free to schedule a no-obligation discovery call.
How does Access Management differ from Identity Management?
Identity Management determines, who a digital identity is and how it is managed. Access Management defines, what permissions this identity possesses – i.e., which applications, systems, or data can be accessed. Identity and Access Management work together but constitute two clearly separate areas of responsibility.
How detailed can permissions and roles be mapped in Bare.ID?
Bare.ID supports an extended RBAC model where roles can be defined globally or application-specifically. Roles contain clearly defined permissions for applications, functions, and resources, and enforce them at the platform level. This allows for consistently mapping very fine-grained access structures without requiring extensive manual rule sets.
How does role-based access control (RBAC) work?
Bare.ID supports a highly flexible RBAC model with global and application-specific roles. Users receive roles directly or through group memberships. Roles can also be assigned for a limited time.
Can group assignments be automated?
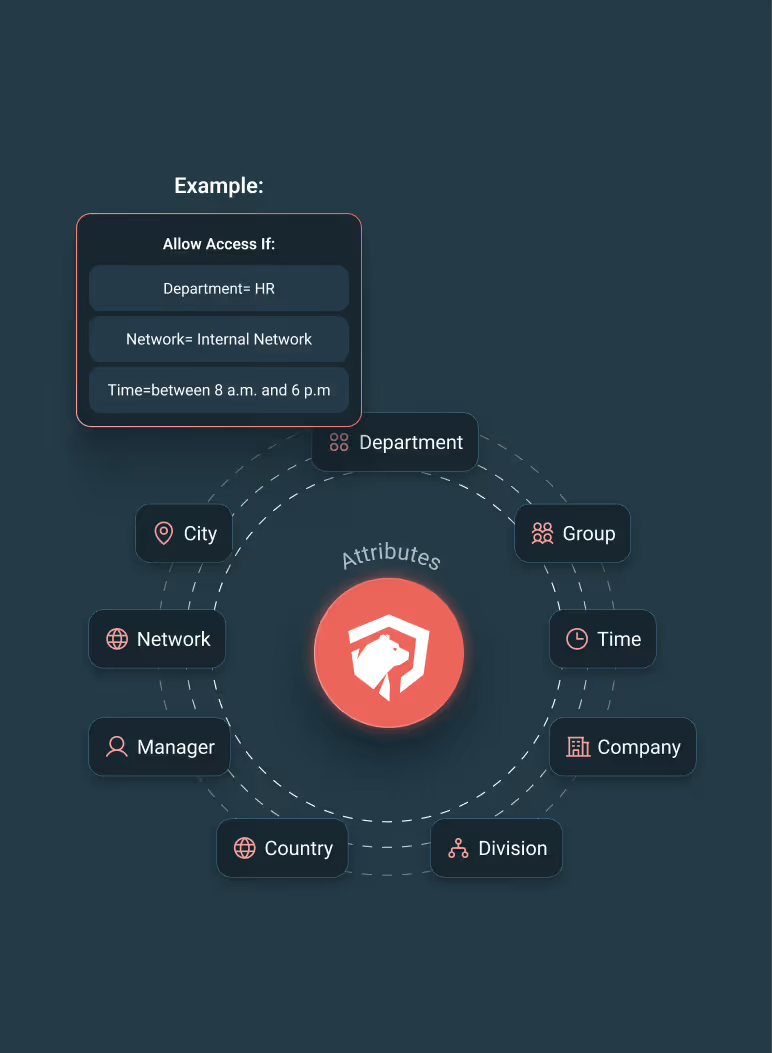
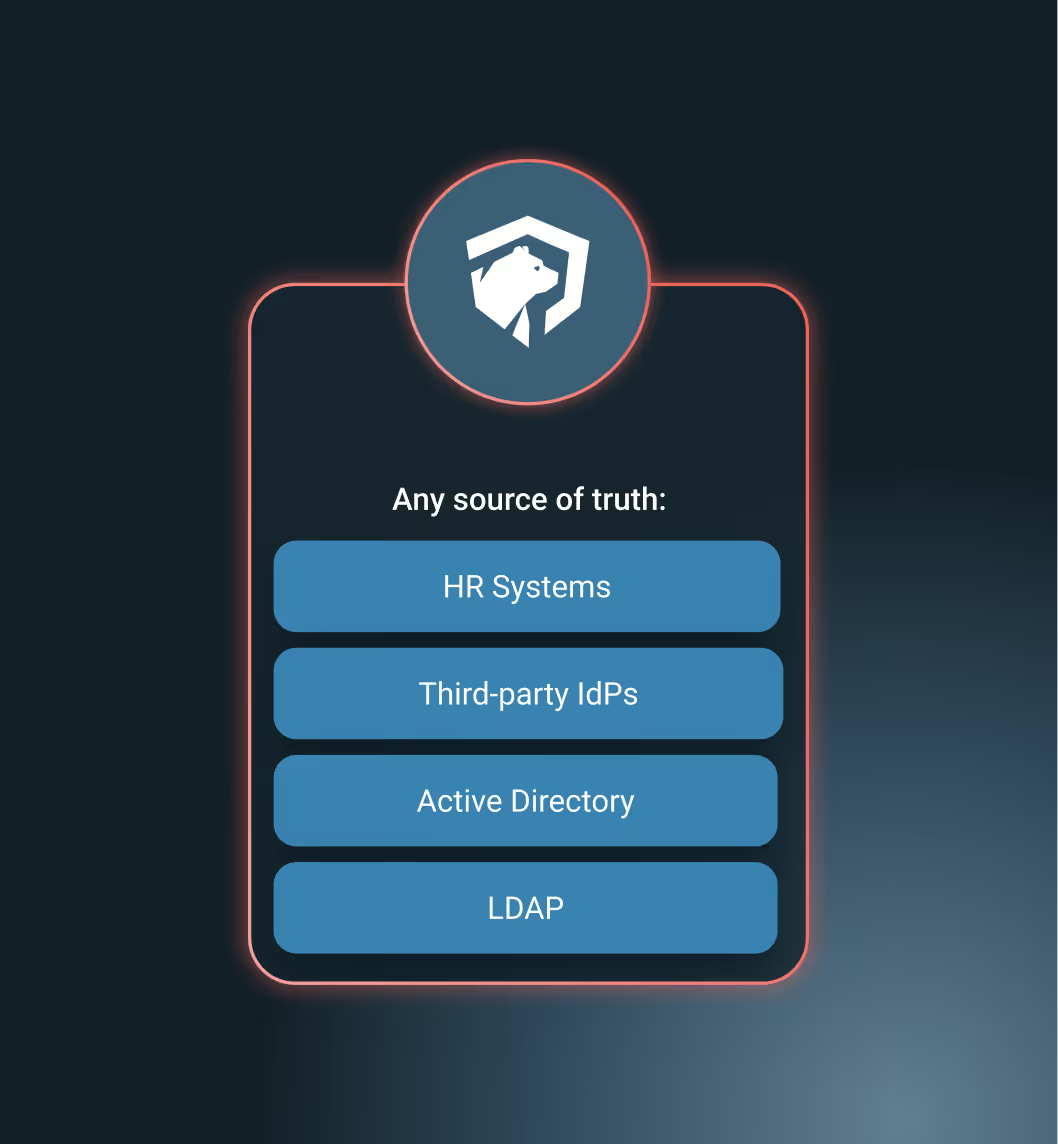
Yes, Attribute-based Access Control (ABAC) allows users to be automatically assigned to groups based on attributes such as department, location, or project affiliation. The rules are defined and managed via a policy engine.
Can Bare.ID block access from specific regions?
Yes, geo-blocking can automatically block login attempts from specific countries or regions. This is particularly important for complying with export control regulations or protecting against attacks from high-risk countries.
Can insecure passwords be blocked?
Yes, Bare.ID implements comprehensive password policies: minimum length, complexity, expiration times, history. Integration with "HaveIBeenPwned" checks whether passwords appear in known data breaches.
How are regular role and permission reviews conducted in Bare.ID?
Bare.ID supports access reviews with automatic reminders. Responsible parties are regularly prompted to review and confirm permissions. Unconfirmed access can be automatically revoked.
Can administrators define different security policies for departments or locations?
Yes. Policies such as password rules, session lifetime, MFA requirements, or device approvals can be configured differently for each department, location, tenant, or user group. This allows, for example, for higher security requirements to be enforced for critical teams.
How does Access Management support audits?
Bare.ID logs all audit-relevant events in an audit-proof manner, including role changes, group changes, policy adjustments, successful and failed login attempts, and application access. This data is structured and readily available for audits. Automatic reports and regular recertifications provide verifiable evidence for your external audits (e.g., GDPR, ISO27001, NIS2) and internal control processes.
Does Bare.ID support delegated management of permissions?
Yes. Bare.ID enables delegated administration, allowing departments to manage roles and groups themselves within predefined guidelines. Administrators control which roles, groups, or authorization areas are delegable, ensuring that IT retains control and that security and compliance requirements are consistently met.
Schedule a free initial consultation now.
It's that simple:














.svg)




