
Modern MFA instead of unnecessary login hurdles
Discover Multi-Factor Authentication with Bare.ID. Adaptive and passwordless login methods ensure high security without slowing down your users.
An additional factor – no additional effort.
No more "Hello123" as a security risk. Classic passwords are insecure and burden users and IT alike. Secure access today requires more than just a password. The integrated Multi-Factor-
Authentication is therefore an essential function of Bare.ID's IAM platform – from classic factors to passwordless methods. This way, you reduce risks without compromising user convenience.

The advantages at a glance
Centrally managed security
With Bare.ID, Multi-Factor Authentication is managed centrally instead of within each application. Security rules can be easily and consistently implemented across all applications.
Contextual protection
Bare.ID strategically deploys additional factors – but only where they truly make sense. Sensitive access is more strongly protected, while everyday logins remain convenient. We combine convenience and security.
Scalably integrated
With Bare.ID, MFA is not a paid add-on, but an integral part of the IAM platform. This allows the security architecture to flexibly grow with new applications and requirements.
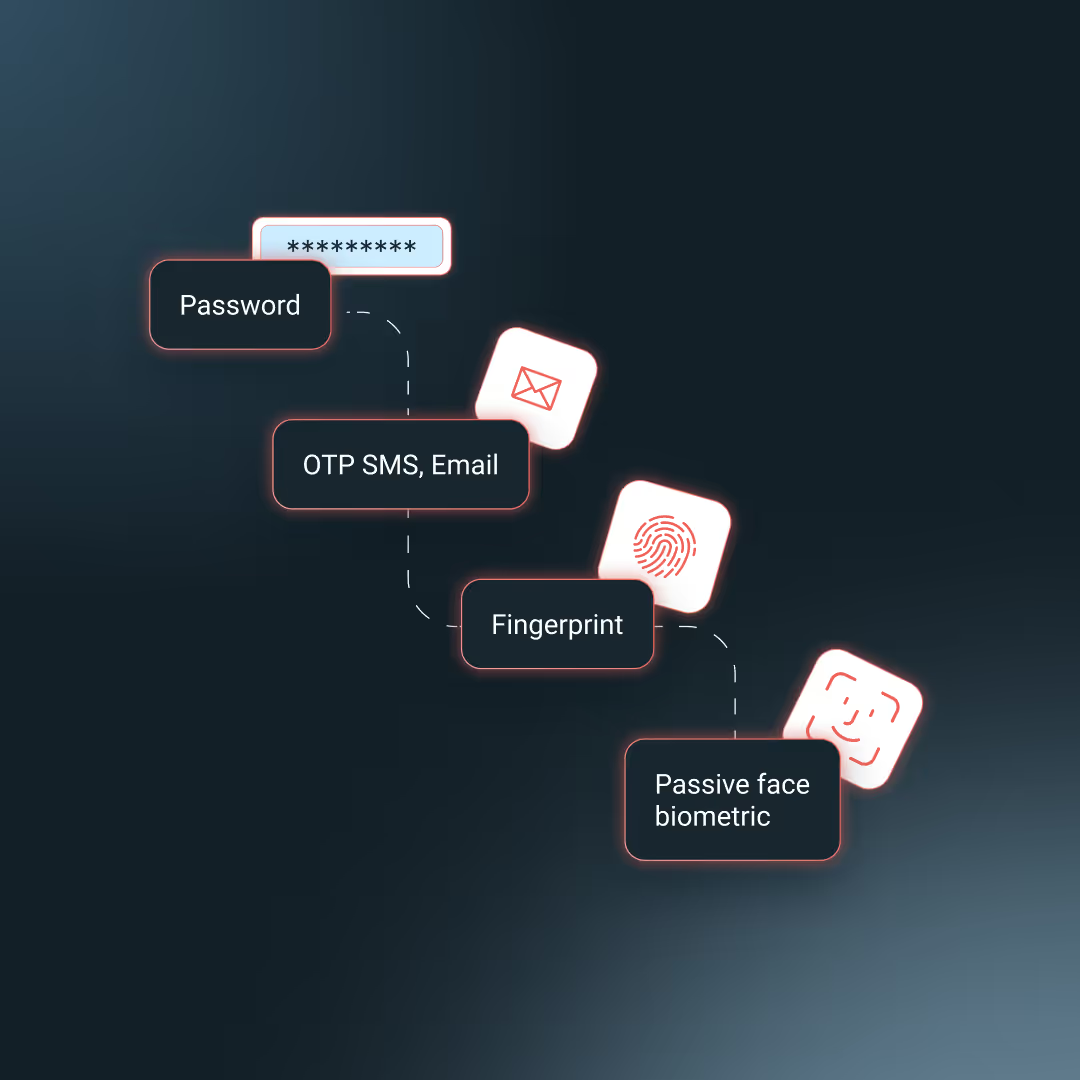
What is Multi-Factor Authentication?
Multi-Factor Authentication (MFA) is a central security mechanism in modern IT environments. It reliably protects access, even if a password is compromised – and is now an integral part of common security standards and regulatory requirements like NIS-2.
MFA is based on three factors: Knowledge – something only the user knows (e.g., password or PIN)
Possession – something only the user has (e.g., smartphone, token, smart card)
Biometrics – something the user is (e.g., fingerprint, facial recognition)

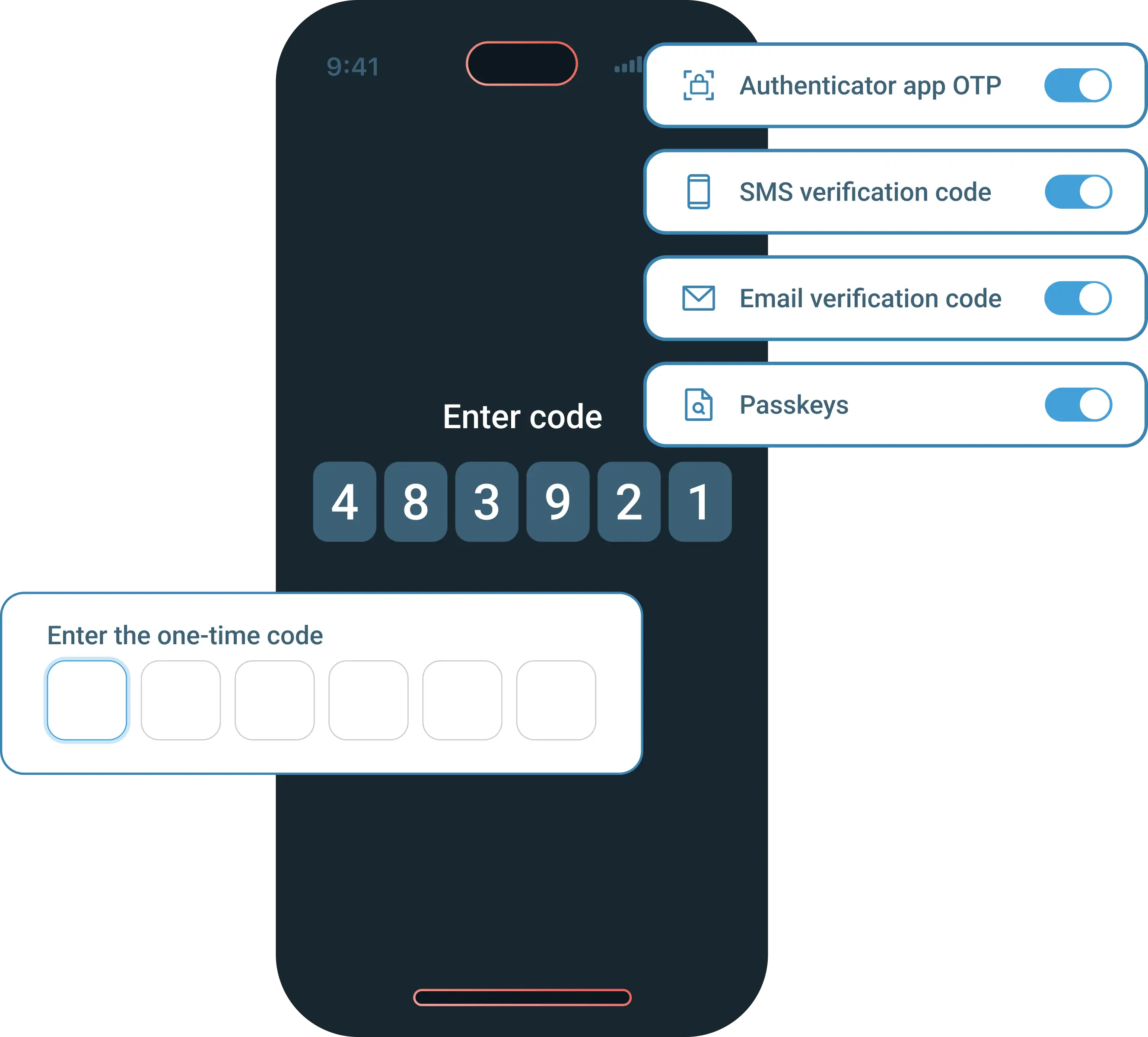
All methods at a glance
Passkeys – log in securely. No password required.
Passkeys are the new gold standard for authentication – phishing-resistant and passwordless. Bare.ID supports secure authentication with passkeys and flexibly integrates them into existing login flows. The transition is seamless for users: passkeys can be activated directly during login – without interrupting the login experience.
Even more convenience.
Even more security.

Features at a glance
All processes can be controlled centrally and managed by users themselves if desired — for an MFA setup that combines security and everyday usability.
MFA with Bare.ID
Multi-factor authentication: added value instead of burden
When login data is no longer a business risk



Put an end to NIS-2 panic.



Introduce MFA.
With no extra load.



Compliance pressure? No problem with Bare.ID.
Bare.ID ensures that identities, access, and authentication processes comply with regulatory requirements. We cover all relevant requirements from GDPR, ISO27001, NIS-2 and DORA in the area of Identity & Access Management. This makes compliance a completed task — instead of an ongoing project on your to-do list.

ISO 27001:2022
Certified

DORA
Compliant

GDPR
Compliant

NIS 2
Compliant
Interest sparked?
Let us talk.

Blog articles, case studies & more
FAQs
Do you have any further questions? Feel free to arrange a non-binding discovery call.
Which MFA methods does Bare.ID support?
Bare.ID supports a wide range of MFA methods: hardware tokens (e.g. YubiKey, FIDO2, WebAuthn), passkeys, TOTP/HOTP (authenticator apps), SMS codes, email codes, push notifications, biometrics, and client certificates. The methods can be combined and activated depending on security requirements.
How does authentication via passkeys or hardware factors such as RFID work?
Passkeys are based on FIDO2/WebAuthn and enable passwordless login via biometric features or hardware keys. RFID cards can be connected via compatible readers as an additional factor.
Is a mixed MFA landscape possible in Bare.ID?
Yes Different user groups can use different MFA methods. For example, administrators can use hardware tokens while employees work via an authenticator app. The selection is based on groups or policies.
How granular can MFA be controlled depending on the user group or application?
Bare.ID provides fine-grained MFA policies based on user groups, roles, applications, or context (IP address, device, location). For example, MFA can only be enforced for critical applications or when accessed from outside the corporate network.
Does Bare.ID support adaptive or risk-based MFA?
Yes Bare.ID can assess the risk of a login and dynamically decide whether MFA is required. Factors such as unusual login times, new devices, or suspicious IP addresses can automatically trigger additional security checks.
Can users manage their MFA methods themselves?
Yes The self-service portal allows users to add, change, or remove MFA methods — depending on applicable policies. You can also configure backup methods and register trusted devices
What happens if a user loses their device or second factor?
There is no risk: Access remains protected via secure processes (e.g. identity verification, temporary replacement factors). Optionally, a replacement is even possible in user self-service — depending on the policy. Bare.ID documents every step in an audit-proof manner — this also ensures compliance.
How does Bare.ID support MFA compliance requirements such as NIS-2?
Bare.ID meets the requirements for strong authentication, as required by NIS-2 as a mandatory security measure, among others. MFA can be enforced consistently for all applications and user groups and adjusted to different security levels via policies.
How can MFA be combined with passwordless logins?
Bare.ID supports passkeys (FIDO2/WebAuthn) and enables completely passwordless logins. MFA is retained because the second factor is technically represented in the ownership or biometric factor of the device. Users don't have to enter a password, and security remains consistent with strong two-factor authentication.
How can the acceptance of MFA be increased among employees or customers?
Bare.ID supports adaptive MFA so that additional factors are only queried when the risk is increased. In addition, suitable, convenient procedures can be defined depending on the user group. Central single sign-on eliminates the need to use different MFA processes per application — MFA remains secure but convenient in everyday life.
Schedule a free initial consultation now.
It's that simple:



















.svg)




